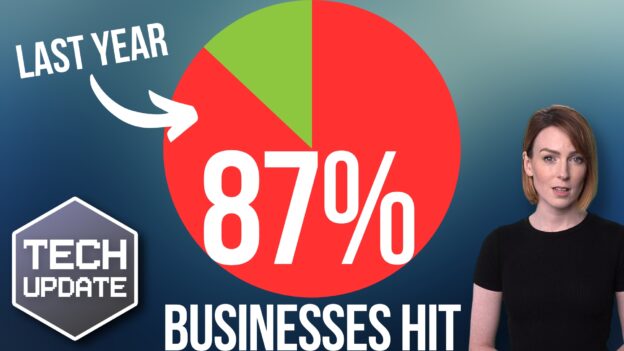
What would you do if your business suffered a ransomware attack tomorrow? Do you have a contingency plan in case of a tornado, hurricane, or earthquake? The unexpected can happen anytime, and small businesses can get hit particularly hard.
Small businesses are the backbone of many economies. They are critical for job creation, innovation, and community development. But running a small business comes with significant risks. This includes financial uncertainty, market volatility, and natural disasters.
60% of small businesses fail within 6 months of falling victim to a cyber-attack.
Thus, small business owners must prepare for the unexpected. This is to ensure their longevity and success. In this article, we will discuss some tips to help small businesses get ready for anything.
Tip 1: Create a Contingency Plan
One of the most critical steps in preparing for the unexpected is to create a contingency plan. A contingency plan is a set of procedures that help a business respond to unforeseen events. Such as natural disasters, supply chain disruptions, or unexpected financial setbacks.
The plan should outline the steps the business will take in the event of an emergency. Including who will be responsible for what tasks. As well as how to communicate with employees, customers, and suppliers.
Tip 2: Maintain Adequate Insurance Coverage
Small businesses should always maintain adequate insurance coverage. This protects them from unexpected events. Insurance policies should include things like:
- Liability coverage
- Property damage coverage
- Business interruption coverage
- Data breach costs
Business interruption coverage is particularly important. It can help cover lost income and expenses during a disruption. Such as a natural disaster or supply chain disruption.
One of the newer types of policies is cybersecurity liability insurance. In today’s threat landscape, it has become an important consideration. Cybersecurity insurance covers things like costs to remediate a breach and legal expenses.
Tip 3: Diversify Your Revenue Streams
Small businesses that rely on a single product or service are at greater risk. Unexpected events can cause them significant harm. Something like a raw material shortage could cripple an organization without alternatives.
Diversifying your revenue streams can help reduce this risk. It ensures that your business has several sources of income. For example, a restaurant can offer catering services. A clothing store can sell merchandise online as well as its physical location.
Tip 4: Build Strong Relationships with Suppliers
Small businesses should build strong relationships with their suppliers. This ensures that they have a reliable supply chain. This is particularly important for businesses relying on one supplier for their products.
In the event of a disruption, having strong relationships matters. It mitigates the risk of a supplier bankruptcy or supply chain issue. Having supplier options can help reduce the impact on your business.
Tip 5: Keep Cash Reserves
Small businesses should keep cash reserves to help them weather unexpected events. Cash reserves can help cover unexpected expenses. Such as repairs, legal fees, or loss of income. As a general rule of thumb, businesses should keep at least six months’ worth of expenses in cash reserves.
Tip 6: Build Strong Outsourcing Relationships
If business owners try to do everything in house, they’re at higher risk. For example, if a key IT team member quits. In this case, the company could face major security issues.
Build strong outsourcing relationships with an IT provider and other critical support services. If something happens to a company’s staff or systems, they have a safety net.
Tip 7: Check Your Financials Regularly
Small business owners should check their finances regularly. This is to ensure that they are on track to meet their goals and to identify any potential issues early on.
This includes:
- Tracking income and expenses
- Creating and reviewing financial statements
- Regularly meeting with a financial advisor
Tip 8: Invest in Technology
Investing in technology can help small businesses prepare for unexpected events. For example, cloud-based software can help businesses store their data off-site. This ensures that it is safe in the event of a natural disaster or cyber-attack. Technology can also help businesses automate processes. Automation reduces the risk of errors and improves efficiency.
Tip 9: Train Employees for Emergencies
Small businesses should train their employees for emergencies. This helps ensure that everyone knows what to do in the event of an unexpected event.
This includes training for natural disasters, cyber-attacks, and other emergencies. Businesses should also have a plan for communicating with employees during an emergency. As well as ensure that everyone has access to the plan.
Tip 10: Stay Up to Date on Regulatory Requirements
Small businesses should stay up to date on regulatory requirements. This helps ensure that they are compliant with all laws and regulations. This includes tax laws, labor laws, and industry-specific regulations. Non-compliance can result in fines, legal fees, and damage to your business’s reputation.
In conclusion, small businesses face many risks. But by following these tips, they can prepare themselves for the unexpected.
Improve Business Continuity & Disaster Preparedness
Get started on a path to resilience and protect your business interests. We can help you prepare for the unexpected. Give us a call today to schedule a chat.
—
Featured Image Credit
This Article has been Republished with Permission from The Technology Press.